Samsung takes first in U.S. AI cyber competition
Samsung Electronics became the winner of the world-class AI security technology competition
“AI Cyber Challenge” (hereinafter referred to as AIxCC) in history. With a $22.5 million prize pool crowdfunded by the U.S. Defense Department’s DARPA, the finals went down Sunday, Aug. 8 at DEF CON 33 in Las Vegas.
Revolutionizing Cybersecurity
Samsung Research, together with Georgia Tech, KAIST and POSTECH as Team Atlanta, have thus developed a new AI security technology. This system, capable of detecting and repairing software vulnerabilities automatically without human intervention, topped global tech rivals and academic institutions.
Unprecedented Achievement
During the semi finals, Team Atlanta was the only one to find an attractive bug outside of their defined competition boundaries.
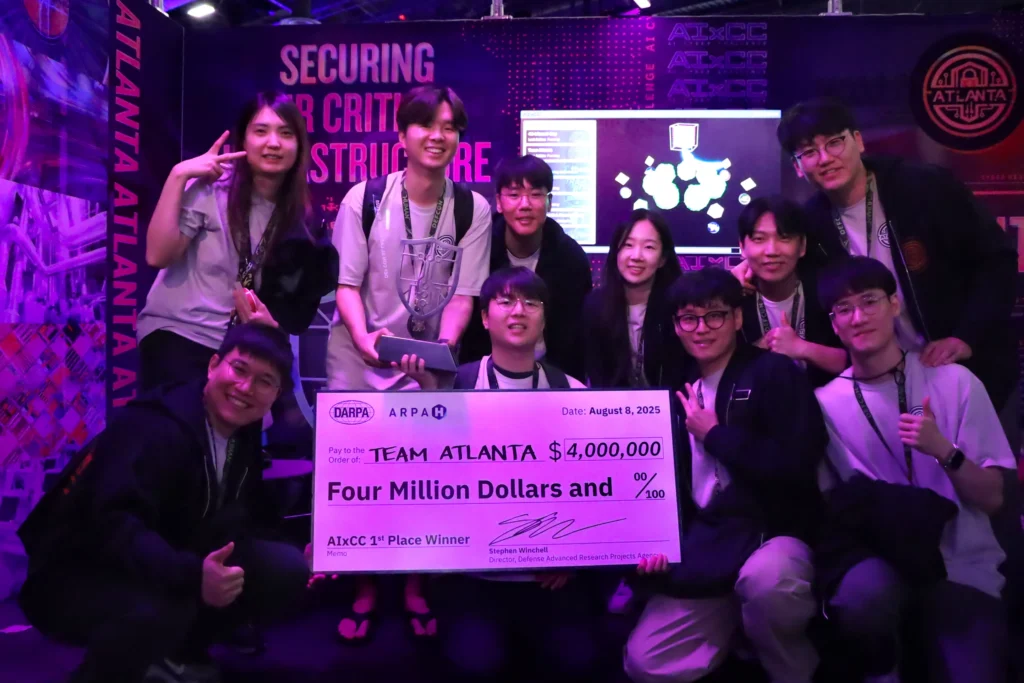
The AIInspect security technology was used to examine source code during finals, where it could detect applied patches with nearly perfect accuracy. Dubbed “Next-Generation AI Cybersecurity for Smartphones,” Samsung and its technology went on to receive the $4 million grand prize along with world-wide recognition.
Why This Matters
Samsung provided our AI security tech at a world-class level, VP Taesoo Kim said. And it will expedite the rollout of self-defending Samsung products.
The two-year challenge affirms Samsung as the top AI security technology provider. Their solution addresses critical gaps:
- Zero-day vulnerability detection
- Real-time AI-powered patching
- Scalable protection for IoT/cloud systems
The Future of AI Security
The South Korean giant wants to roll out this AI security tech into its ecosystem. AI security tech from smartphone to infrastructure that will neutralize threats autonomously, and change how we protect digital assets.
FAQ
A US Defense Department contest to help develop AI security tech that self-heals vulnerable code ($22.5M)
Code has been scanned for vulnerabilities (including ones that were not intended!), and patched without any human input at all.
Anyone can then try to use this info in consumer tech or enterprise solutions for threat hunting.